On 26/3, the Hanoi People's Court sentenced Nguyen Xuan Hai, Ta Anh Truong, and Le Quang Khai, all born in 2005 and residing in Hai Phong, along with Nguyen Tuan Canh, born in 1996, to 13-15 years in prison each for property appropriation fraud.
The case began in July 2024 when the four unemployed young men were invited by a compatriot named Nguyen Chi Cong (born in 2000) to Cambodia to "perform biometric transfer transactions" with a salary of up to 25 million VND per month.
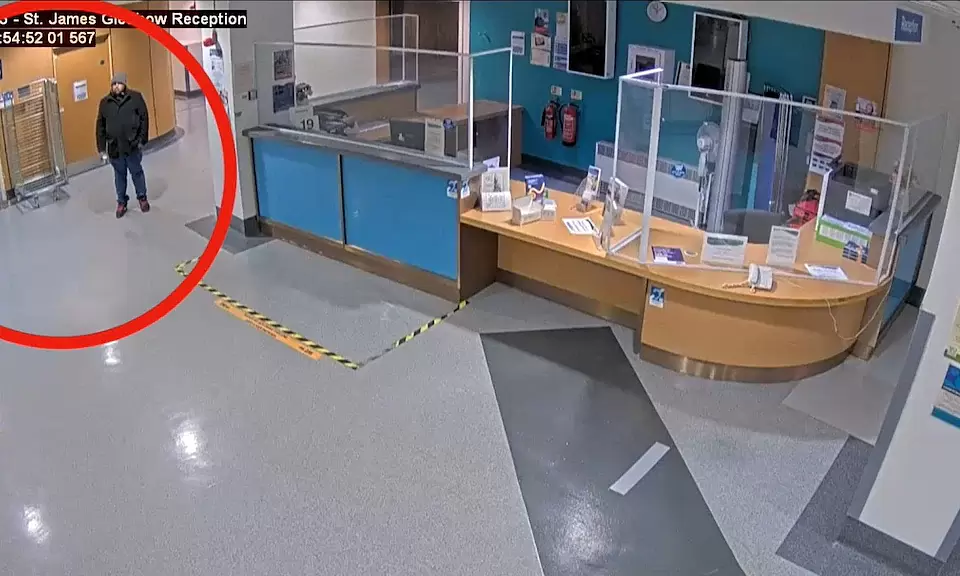
 |
_The defendants in court. Photo: Danh Lam_
Before leaving Vietnam, following Cong's instructions, the four defendants opened numerous bank accounts for their future operations.
On 22/7/2024, the group entered Cambodia via an unofficial route at the Moc Bai border gate in Tay Ninh. They were then transported by motorbike taxi to a building called "Tam Thai Tu," where they were managed by a group of Chinese individuals. Their personal phones were confiscated, and they were provided with bank accounts, OTP codes, and a detailed scam script.
The four individuals worked in two shifts, putting in 15 hours each day.
**Four-step scheme to manipulate victims**
The fraud scheme operated by this syndicate at the "Tam Thai Tu" complex involved four distinct stages, beginning with approaching victims by impersonating official agencies.
The group of four defendants was tasked with making calls, pretending to be post office employees announcing failed package deliveries or impersonating police officers from various levels (commune, ward, district) and even public administration center officials.
The calls typically informed victims that they were involved in ongoing criminal investigations or required urgent administrative procedures, such as updating Citizen Identification Card (CCCD) information, registering for level 2 electronic identification, or declaring vehicle identification details on the public service system.
Once initial trust or fear was established, the scam group moved to the next stage: luring victims to access fake links.
These links had domain names that closely resembled official government portals, public service portals, or residency registration sites.
Victims were instructed to download and install applications with names similar to legitimate ones. These applications, in reality, contained malicious code that allowed the fraudsters to collect data and remotely control the victim's device.
The third stage focused on deep information gathering and taking control of bank accounts. After the application was installed, victims were prompted to enter detailed personal information, account numbers, and online banking login credentials.
To finalize control and collect authentication methods, the fraudsters would ask victims to perform a very small money transfer, typically only 10,000-12,000 VND, under the guise of a "processing fee" or "service fee."
While victims performed the authentication steps to pay this small amount on their compromised phones, the scam group recorded all necessary information to log into the account from another device.
The final and decisive stage involved seizing assets through biometric technology.
At this point, the Chinese operators would log into the victim's account and initiate commands to transfer all existing funds to other accounts. When the banking system requested facial authentication to approve the transaction, the defendants directly performed the face scan (biometric authentication) as prompted by the application on their own devices to complete the transfers.
The stolen money was transferred to the accounts the defendants had opened in Vietnam, then circulated through multiple accounts of service companies to obscure the trail and erase evidence.
One of the most notable cases involved Ms. Anh, a resident of Hanoi. On 4/10/2024, Ms. Anh was deceived by one of the defendants, who impersonated a Kien Hung ward police officer, into installing an application to process a Citizen Identification Card for her child.
Believing the scammer, she logged into her bank account and performed facial authentication. As a result, nearly 2 billion VND from her bank account vanished after four consecutive transfers to defendant Hai's account.
Investigators determined that in just one month, from 22/7/2024 to 22/8/2024, this syndicate successfully carried out 28 fraud cases, embezzling 19.3 billion VND from 23 victims nationwide. The use of international servers and domain names beyond the direct control of domestic authorities was a sophisticated tactic aimed at prolonging tracing time and complicating investigations.
Moreover, after being stolen, the money did not remain in the defendants' personal accounts but was "cycled" through numerous intermediary accounts before flowing into corporate accounts.
When police investigated, most of these companies were not operating at their registered addresses, or their legal representatives were individuals not present locally, with some even unaware that their personal information had been used to establish a business.
As for Cong, the individual who brought the defendants to Cambodia, he is currently absent from his residence, so the investigating agency has separated his case for later processing.
Hai Thu